Before you go, You might interested on our cloud edition.
LIMITED TIME OFFER!
Switch and upgrade to cloud edition today and get 10% off on monthly plan and 20% off in annual plan.
Benefits
- Advanced Features Access
- Third-party tools and apps integration
- Unlimited storage & automatic backups
- Data security and compliance
- Access from anywhere & anytime
- 24/7 Priority Support
How It Works
Elevate your project management experience with our project management tool user-friendly design with powerful features, to take control of your projects from start to end.
Create, Plan, Prioritize, assign projects and Organize tasks.
Organize Tasks and Workflows for greater productivity. Simplify project management for easier project execution and delivery. Drive team communication across all departments. Plan, track and monitor projects from a single page.
Try Orangescrum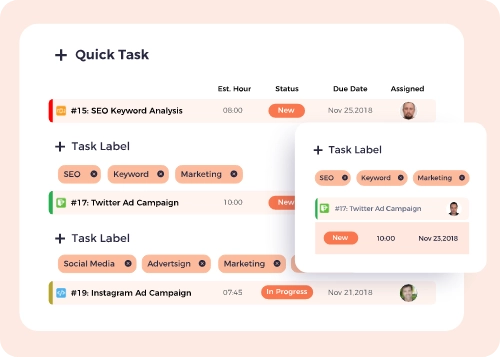
Centralize project information for easy access and manage your daily activities.
Orangescrum brings transparency to project development processes across all departments. Track, visualize and streamline each real time activities of team and projects and get higher project visibility, stay focused on goals, projects and daily tasks.
Try Orangescrum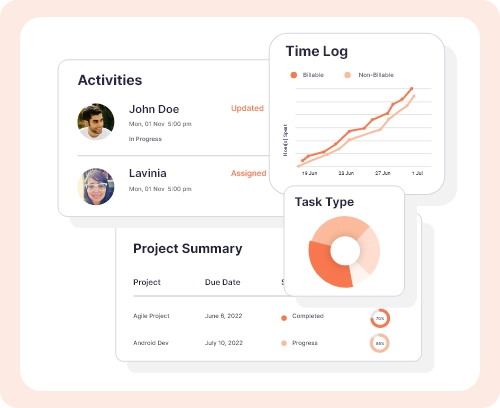
Share & Receive progress in real time with your customers.
Get real-time updates on your project development and team. Get a complete view of your projects to plan your project workflows more effectively.
Try Orangescrum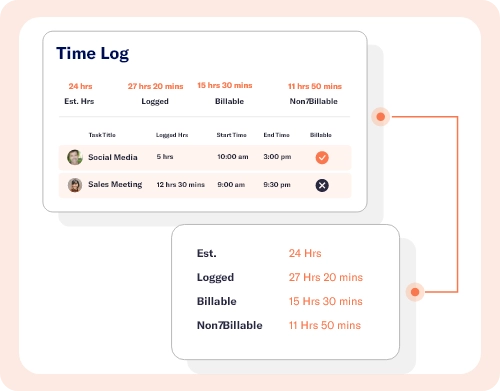










Opensource Vs Cloud Vs Self Hosted

20%
OFF
- Get 10% off on cloud edition monthly plan upgrade.
- Get 20% off on Self-hosted annual plan upgrade.
Thousand of companies trusted over Orangescrum
More than million users showing their interest with Orangescrum open source project management software